In recent years, we have presented How to Spoof PDF Signatures and Shadow Attacks: Hiding and Replacing Content in Signed PDFs, which describe attacks on PDF signatures under various attack scenarios. The attacks focused on so-called approval signatures. However, in addition to signing PDFs, the PDF specification also specifies the certification of documents, also known as certification signatures.
To close this research gap, we performed an extensive analysis of the security of PDF certification. In doing so, we developed the Evil Annotation Attack (EAA), as well as the Sneaky Signature Attack (SSA). The attack idea exploits the flexibility of PDF certification, which allows signing or adding annotations to certified documents under different permission levels. Our practical evaluation shows that an attacker could change the visible content in 15 of 26 viewer applications by using EAA and in 8 applications using SSA by using PDF specification compliant exploits. We improved both attacks' stealthiness with applications' implementation issues and found only two applications secure to all attacks.
PDF Structure and Basics
The PDF specification additionally defines interactive elements that allow user input into the document. Such elements are separated in two categories: forms and annotations.
Forms. PDF forms allow user input in a predefined mask, such as a text field, a radio button, or a selection box. Facilities, such as the administration, usually use forms to create PDF documents with predefined areas which are intended to be filled out by users. The user input is, however, limited to the defined form fields and cannot change other content within the PDF.
Annotations. Annotations introduce a different method for a user input by allowing a user to put remarks in a PDF document like text highlighting, strikeouts, or sticky notes. Annotations are not limited to predefined places within the PDF and can be applied everywhere within the document.
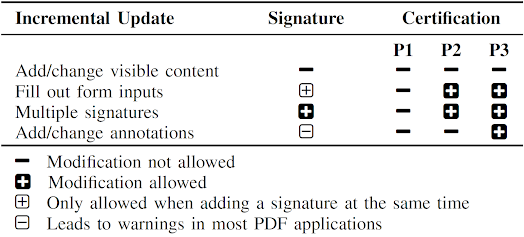
An Incremental Update introduces a possibility to extend a PDF by appending new information at the end of the file, see Inc. Update 1 in the figure above. In this way, the original document stays unmodified and a revision history of all document changes is kept. Each Incremental Update defines new objects, a new xref table, and a new trailer. An example of an Incremental Update is the inclusion of an certification, signature, annotation, or the filling out forms within a PDF.
UI-Layer 1: Top Bar Validation Status. UI-Layer 1 is usually displayed immediately after opening. Typical applications use a clearly visible bar on top of the PDF content. The status of the certification and signatures validation is provided as a text (e.g., valid/invalid), often combined with green, blue or red background colors, cf. figures in EAA and SSA sections.
Difference between Signed and Certified Documents
By signing a PDF document, a Signature object is created. This object contains the trusted public keys to verify the document, the signature value, the range of bytes that are protected by the signature, and a userfriendly information regarding the signer of the document. The Signature object is usually added to the PDF document by using an Incremental Update.
Certified Documents
P3: In addition to P2, annotations are also allowed.
Evil Annotation Attack (EAA)
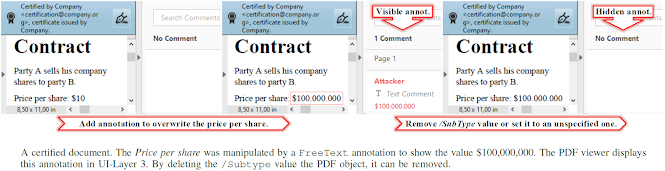
Evaluating Permission P3. According to the specification, the following changes in a certified document with P3 are allowed: 1) adding/removing/modifying annotations, 2) fillingout forms, 3) and signing the document. We started with an in-depth analysis of all annotations and their features. We evaluated 28 different annotations and classified these with respect to their capabilities and danger level. The results are depicted in the Table on the right side and will be further explained.
Danger Level of Annotations. We determined three annotations with a danger level high capable to hide and add text and images: FreeText, Redact, and Stamp. All three can be used to stealthily modify a certified document and inject malicious content. In addition, 11 out of 28 annotations are classified as medium since an attacker can hide content within the certified document. The danger level of the remaining annotations is classified as low or none since such annotations are either quite limited or not allowed in certified documents.
Attacking with Annotations. According to our attacker model, the attacker possesses a validly certified document allowing the insertion of annotations. To execute the attack, the attacker modifies a certified document by including the annotation with the malicious content at a position of attacker's choice. Then, the attacker sends the modified file to the victim who verifies the digital signature. The victim could detect the attack if it manually opens UI-Layer 3 or clicks on the annotation. However, none of the tested PDF applications opened UI-Layer 3 automatically. Additionally, the attacker can lock an annotation to disable clicking on it.
Improving the stealthiness of EAA
Special Modifications
Sneaky Signature Attack (SSA)
The idea of the Sneaky Signature Attack (SSA) is to manipulate the appearance of arbitrary content within the PDF by adding overlaying signature elements to a PDF document that is certified at level P2.
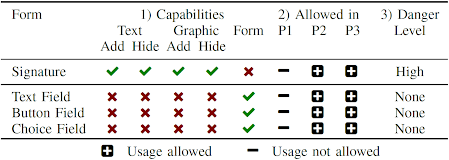
Evaluating Permission P2. According to the specification, the following changes in a certified document with P2 are allowed: filling-out forms, and signing the document. We started the analysis of forms as depicted in the table on the right side and evaluated their capabilities.
Danger Level of Forms. According to our analysis, the danger level was none because the insertion of new form elements, customizing the font size and appearance, and removing form elements is prohibited. The only permitted change is on the value stored in the field. Thus, an attacker is not able to create forms which hide arbitrary content within the PDF document. Surprisingly, these restrictions are not valid for the signature field. By inserting a signature field, the signer can define the exact position of the field, and additionally its appearance and content. This flexibility is necessary since each new signature could contain the signer's information. The information can be a graphic, a text, or a combination of both. Nevertheless, the attacker can misuse the flexibility to stealthy manipulate the document and insert new content.
Attacking with Forms: SSA. The attacker modifies a certified document by including a signature field with the malicious content at a position of attacker's choice. The attacker then needs to sign the document, but he does not need to possess a trusted key. A self-signed certificate for SSA is sufficient. The only restriction is that the attacker needs to sign the document to insert the malicious signature field. This signing information can be seen by opening the PDF document and showing detailed information of the signature validation. In this case, the victim opening the file can get suspicious and refuse to accept the document, even though the certification is valid.
Improving the stealthiness of SSA
Evaluation
Authors of this Post
Vladislav Mladenov
Christian Mainka
Jörg Schwenk
Acknowledgments
More information
- Hacker Tools For Windows
- Pentest Tools For Android
- Pentest Tools Find Subdomains
- Pentest Tools Online
- Hacker Security Tools
- Hacking App
- Pentest Tools List
- Pentest Recon Tools
- Pentest Tools Url Fuzzer
- Pentest Tools Review
- What Are Hacking Tools
- Hacker Tools For Ios
- Pentest Tools Open Source
- Hacker Security Tools
- Hacker Tools List
- Hacking Tools Hardware
- Pentest Tools Apk
- Nsa Hack Tools
- Hacking Tools For Kali Linux
- New Hack Tools
- Hacker Tools Free Download
- Hacker Tool Kit
- Hacking Tools Software
- Pentest Reporting Tools
- Tools Used For Hacking
- Hacks And Tools
- What Is Hacking Tools
- Hack Rom Tools
- Hacking Tools Hardware
- Hacker Tools Software
- Hacker Tools
- Hacker Tools Free
- Hacking Tools Windows 10
- Hacking Tools Usb
- Hacking Tools 2020
- Usb Pentest Tools
- Pentest Recon Tools
- Hacker
- Hack Tools
- Hacking App
- Hacking Tools For Windows 7
- Android Hack Tools Github
- Pentest Tools Online
- Hacker Tools 2020
- Pentest Tools Find Subdomains
- Hacking Tools For Mac
- Nsa Hacker Tools
- Pentest Tools Framework
- Computer Hacker
- Hacking Tools Hardware
- Hackrf Tools
- Termux Hacking Tools 2019
- Hacking Tools And Software
- Nsa Hacker Tools
- Hacker Tools 2019
- Pentest Tools Apk
- Hack Website Online Tool
- Termux Hacking Tools 2019
- Blackhat Hacker Tools
- Growth Hacker Tools
- Pentest Tools Subdomain
- Hacking Tools Software
- Android Hack Tools Github
- Computer Hacker
- Hacking Tools Hardware
- Hacking Tools Free Download
- Hack Tools For Pc
- Hacking Tools 2020
- Hack Tools Mac
- Hacking Tools Software
- Pentest Tools Subdomain
- Hacker Tools Apk
- How To Hack
- Hacking Tools Online
- Hack Tools Pc
- Pentest Tools Url Fuzzer
- Hack Tools 2019
- Nsa Hack Tools
- Best Pentesting Tools 2018
- Pentest Tools Android
- Pentest Tools
- Hacking Tools For Pc
- Hacker Tools Online
- Pentest Tools Windows
- Hack Tools Mac
- Hacking Tools Software
- Install Pentest Tools Ubuntu
- Easy Hack Tools
- Hacker Tools For Ios
- Hacker Tools For Mac
- Beginner Hacker Tools
- Nsa Hack Tools
- Nsa Hacker Tools
- Hacker Tools 2019
- Pentest Tools For Ubuntu
- Hacker Tools Apk Download
- Hak5 Tools
- Hacking Tools Online
- Hacking Tools For Games
- Hacker Tools Software
- Hacking Tools Github
- Hacking Tools Hardware
- Pentest Tools Port Scanner
- Hacker Security Tools